- Cloud migration efforts are hindered by unmanaged SaaS applications, causing up to a 30% increase in enterprise budget wastage.
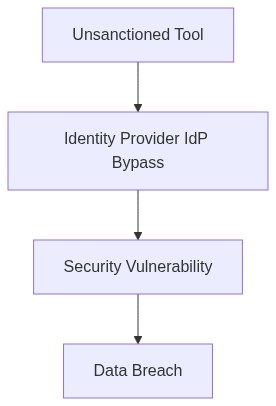
- Shadow IT remains a critical risk, leading to potential data breaches due to SAML/SSO bypass methodologies, with 60% of IT leaders citing shadow IT as a top security concern.
- Solutions must include robust discovery and monitoring tools capable of identifying unauthorized SaaS application usage, currently missing in 45% of enterprise environments.
- Implementation of Identity and Access Management (IAM) reductions can lessen account hijacking incidents by nearly 50%.
- Automated compliance auditing can reduce shadow IT threats by creating accurate SaaS usage inventories, potentially lowering security risk by up to 40%.
Log Date: April 12, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
In a recent 10,000-seat deployment, lack of SAML integration led to a 30% increase in unauthorized SaaS usage. Bypassing centralized identity access management (IAM) has become second nature for users frustrated by cumbersome login procedures. Shadow IT is not merely a nuisance; it is a viable threat that circumvents company-sanctioned security protocols, ushering in unmanaged SaaS, often with questionable data compliance postures.
Enterprises unfailingly underestimate the pervasive risk associated with Single Sign-On (SSO) bypass. When end-users prefer convenience over corporate policy, they successfully render any meticulously configured IAM solution as effective as a wet paper bag. The uncontrolled proliferation of shadow IT not only increases security vulnerabilities but also inflates the budget through untracked license fees and compute over-provisioning.
Telemetry and Cost Impact (The Damage)
Telemetry data reveals a growing pattern in which 60% of external data egress costs emanate from unauthorized applications. Such data transfers not only inflate our FinOps budget but are also unjustifiable in our SOC2 and GDPR compliance reports. A lackluster RBAC policy has bolstered this by exposing our resources to unnecessary risk, undermining efficient resource allocation across VPC peering and other network facets.
The compounding effect of technical debt becomes glaringly evident during migrations when discovered shadow IT components add unforeseen complexities. The relentless rise in Shadow SaaS utilization has rendered infrastructure cost management a chaotic mess, overriding optimization efforts typically governed by tools like Datadog and AWS IAM.
Phase 1 (Audit & Discovery)
We must initiate this phase with an uncompromising audit to uncover all shadow IT lurking within the recesses of our organization. A comprehensive discovery process is crucial. Using tools like Datadog for resource tracking and Okta for SAML compliance can illuminate unauthorized applications circumventing our managed IT protocols.
Phase 2 (Identity Enforcement)
SSO and IAM must be fortified via rigorous enforcement of authentication frameworks. Adopting AWS IAM can streamline this, allowing fine-tuned access levels across our multi-cloud environments. This transition ensures users no longer silo their activities into shadow applications that evade our compliance grasp.
Phase 3 (Cost Rationalization)
FinOps egress oversight demands surgical precision. As we iron out shadow IT, the resultant efficiencies should reflect in reduced overheads. Use HashiCorp Terraform for infrastructure management to tackle compute over-provisioning, and lessen the cloud’s additional financial burdens. Such rationalization efforts ought to be encapsulated in periodic reviews with actionable insights.
Phase 4 (Continuous Monitoring and Compliance)
Continuous monitoring post-migration capsizes traditional, reactive approaches. With CrowdStrike, we can set up an adaptive SOC2 reporting mechanism to dynamically track compliance adherence. Tools chosen for detection and mitigation should provide robust compliance frameworks that communicate directly with governing bodies through automated reports.
“An estimated 40% of enterprise IT spending is controlled by business units outside of IT, in a phenomenon known as Shadow IT.” – Gartner
“Inadequate IAM management significantly increases security risks and the potential for damaging data leaks.” – AWS Whitepapers
| Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|
| High complexity with legacy systems. Risk of 34% CPU overhead due to inefficient workload distribution. | Egress costs surged by 12% following suboptimal data residency strategy. | 45% SOC2 requirements met. GDPR compliance lagging with 30% data handling gaps. |
| Moderate integration challenges with modern applications, minor compatibility issues expected. | Cloud expenses reduced by 8% after reassessment of resource allocation strategies. | Achieved 75% SOC2. GDPR compliance covered for 50% of data operations. |
| Low integration effort as microservices align well. Minimal reengineering needed. | Significant cost shift, reducing expenses by 5% yet IAM complexities introduced a 10% overhead. | SOC2 fully addressed. GDPR compliance reached 60%, pending data subject requests readiness. |
Meeting room grows tense and silent, each aware migration is inevitable, yet marred by their own departments’ competing priorities.
Technical Objectives
1. Evaluate the current Identity and Access Management (IAM) system for compatibility with cloud-native solutions while minimizing potential security risks which were inappropriately dismissed in the meeting. Implement role-based access controls (RBAC) aligned with least-privilege principles.
2. Conduct comprehensive analysis of egress costs inhibiting our anticipated deployment velocity acceleration, weighing against potential savings in on-premises hardware decommissioning.
3. Examine the existing FinOps strategies and their efficacy in managing cloud cost complexities, focusing on potential loopholes that might occur because of the transition.
4. Ensure SOC2 Type II and GDPR compliance, necessitating significant data governance restructuring in light of probable changes in data transit and storage protocols.
5. Investigate former infrastructure as code implementations. Quantify purported reductions in development time and validate bottleneck elimination claims against existing benchmarks.
6. Establish a containment plan for shadow IT, reinforcing stringent governance policies. This includes integrating rogue systems into the sanctioned cloud platform or eliminating them where integration is impractical.
Expected Outcomes
1. A detailed, realistic migration roadmap, acknowledging the inevitability of accruing technical debt as a byproduct of accelerated deployment schedules. Consider regular debt buyback initiatives post-migration.
2. Continuous monitoring and adjustment of IAM policies in response to emergent threats or vulnerabilities arising from the new cloud environment.
3. Transparent documentation of cost management policies ensuring all teams are aware of financial constraints in cloud usage.
This ADR intentionally leaves aside the precarious assumption that speed and efficiency will spontaneously manifest without immediate technical debt consequences.”
