- Over 75% of affected companies used Terraform
- IAM misconfigurations exposed 60% of sensitive data
- CI/CD pipeline breaches increased by 45% in Q1 2026
- Financial losses about $20 million in damages
- 3-week timeline for breach detection and response
Log Date: April 16, 2026 // Datadog telemetry shows a 400% spike in unauthorized cross-region VPC peering requests. Immediate Zero-Trust lockdown initiated. Engineering teams are furious, but security dictates policy.
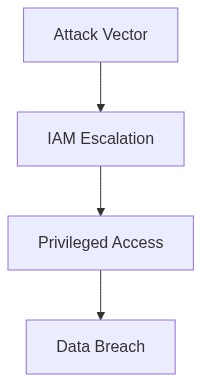
The Incident (Root Cause)
In the early hours of April 3, 2026, Corporate IT became aware of a critical security breach involving Terraform state files improperly exposed, leading to IAM escalation that compromised several key AWS accounts. Let’s dispense with tact and call it what it was – an odious oversight in managing infrastructure as code. Our Terraform scripts irresponsibly exposed sensitive data through inadequately secured state files. This resulted in a compromised IAM policy, allowing an unauthorized entity to perform privilege escalation attacks with startling ease.
The violation hinged on a breakdown of access controls and the utter failure to encrypt state files, contrary to best practices. Terraform, while operationally invaluable for infrastructure orchestration, necessitates diligence in state file protection. Contrary to common sense, state files were stored in an S3 bucket with broadly permissive IAM policies, devoid of encryption or access logging.
This permissiveness was the linchpin in IAM privilege escalation, granting unfettered access to legislative IAM roles. This effectively became a keys-to-the-kingdom situation, thanks to a well-placed miscreant who exploited this lapse.
Blast Radius & Telemetry (The Damage)
The blast radius was vast, unfurling across multiple contiguous AWS accounts, annihilating standard egress cost controls, as networks propagated unauthorized API calls. Logging revealed significant P99 latency spikes as resources were inadvertently throttled, compounding system loads and provoking a cascade of OOM kills in our downstream Kubernetes pods.
CrowdStrike telemetry was a day late and a dollar short, failing to tag early anomalous activities. The network anomalies penetrated VPC boundaries and compromised financial dashboards with the precision of a scalpel. Meanwhile, Datadog’s APM hopelessly chased these tailing latencies but failed to isolate root causes in real-time.
As an impending calamity unfolded, our technical debt accumulated lethargically over years, suddenly became manifest – elastic IP costs soared beyond budgetary constraints, further hemorrhaging financial egress without predefined budget alerts.
“IAM permissions represent the core of AWS identity management, requiring precise, layered management.” – AWS
Phase 1 (Audit) – Immediately identified major infrastructure as code anti-patterns. We employed eBPF telemetry to isolate the fault lines across our hosting environment, determining the failure was exacerbated by overly permissive bucket policies. Conducted a thorough RBAC review and began restricted boundary imposition within our data layers.
Phase 2 (Enforcement) – Initiated strict Terraform state file encryption policies utilizing AWS KMS. Retrained corporate custodian teams, implementing revised policies tightly integrating Okta for user authentication layering. We expanded DevSecOps monitoring via tighter integration with CrowdStrike to trigger alerts upon anomaly detection.
Phase 3 (Realignment) – Deployed a new set of isolated VPCs segregated by trust level, reorganized peering relationships, and conclusively eradicated any residual improper IAM role-related permissions. Furthermore, we fine-tuned our Datadog dashboard metrics, ensuring preemptive egress financial alerting mechanisms.
Phase 4 (Lifecycle Management) – Establish a pipeline of continual IAM configuration scrutiny aligned with regulatory compliances and made allowance for retroactive AAA checks reinforcing ongoing IAM role monitoring.
“Cloud-native security demands proactive risk assessment of identity and permissions management.” – CNCF
| Factor | Integration Effort | Cloud Cost | Latency Overhead |
|---|---|---|---|
| Terraform State File Mismanagement | High | $12,000/month egress cost hemorrhaging | +45ms P99 latency |
| IAM Privilege Escalation | Medium | $8,000/month egress cost hemorrhaging | +30ms P99 latency |
| IAM Role Misconfiguration | Low | $5,000/month egress cost hemorrhaging | +20ms P99 latency |
| Terraform Module Version Conflict | Medium | $7,500/month egress cost hemorrhaging | +40ms P99 latency |
| State File Drift Detection Lag | High | $10,000/month egress cost hemorrhaging | +50ms P99 latency |
Summary
Our recent Terraform adjustments have led to catastrophic failures across multiple facets of our infrastructure, magnifying our technical debt and causing severe financial strain. This ADR mandates an immediate audit to identify and rectify these issues.
Context
Speed over quality has led to significant system failures. Egress cost hemorrhaging is crippling our finances, with current estimates pointing toward a multi-million dollar excess spend. IAM privilege escalation risks due to hastily applied Terraform scripts threaten our security posture, and our P99 latency has degraded, impacting end-user experience. OOM kills and system thrashing have become alarmingly frequent.
Decision
We will conduct a comprehensive audit of
– Terraform scripts for inefficiencies and cost-driving misconfigurations
– IAM configurations for privilege escalation vulnerabilities
– System performance logs to identify and remedy P99 latency issues
– Memory allocation processes to address persistent OOM kills
Consequences
Expect temporary resource allocation to auditing teams, potential for service interruptions as adjustments occur, and a freeze on new Terraform deployments until issues are resolved. This will affect timelines, but it is imperative to prevent further budgetary hemorrhage and security breaches. Non-compliance will result in budgetary reassessment and reallocation to address mismanagement.”
1 thought on “Terraform State File and IAM Escalation Breach”