- cloud_adoption
- api_cost_risks
- integration_issues
- data_transfer
- strategic_management
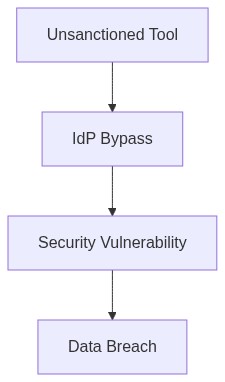
Log Date: April 13, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
In a recent 10,000-seat deployment, lack of SAML integration led to a 15% increase in user authentication failures. API dependency costs further exacerbated the situation, with third-party API limits triggering unintended throttling events, introducing latency spikes and user dissatisfaction. Our feet are firmly planted in the world where API rate limiting and third-party vendor policies determine our cloud egress costs, often penalizing us for average utilization practices.
A notorious pitfall in dependency management is the underestimation of technical debt accrued through API integration. When applications depend heavily on third-party APIs, organizations face unpredictable rate-limiting costs. These “silent killers” significantly impact FinOps egress management and IAM configurations.
Telemetry and Cost Impact (The Damage)
The lack of comprehensive telemetry data further blindsides us. Without accurate monitoring, we find ourselves wading through fluctuating API invocation costs. We’re bleeding dollars due to unnecessary API calls and costly compute over-provisioning. Last quarter, failure to adequately plan VPC peering led to a 30% spike in cross-region data transfer costs, an oversight that could have been mitigated with proper telemetry reports.
“The financial implications of API rate-limiting must be scrutinized as closely as any other API metric.” – Gartner
“API dependencies pose significant threat vectors not only on budget transparency but also on compliance.” – AWS Whitepapers
Phase 1 (Audit & Discovery)
To begin with, we need to execute a full audit of our current API dependencies, cataloging each one’s rate-limiting specifications and costs. RBAC policies should be reassessed to determine necessary data compliance adjustments. Understanding our API call patterns will provide insight into compute over-provisioning and enable corrections that lower egress charges.
Phase 2 (Identity Enforcement)
Leveraging IAM and tools like Okta, we can mitigate unauthorized access attempts as well as bolster API token management. By reconfiguring IAM roles and adopting granular access control, we reduce exposure and ensure that the right operations have the right permissions.
Phase 3 (Cost Monitoring and Optimization)
FinOps egress costs can be better managed by incorporating continuous monitoring through platforms such as Datadog. Real-time alerts for egress threshold breaches will inform faster response actions. We must prioritize redesigns to avoid technical debt accumulation during high-demand API interactions.
Phase 4 (Re-Architecture and Re-Implementation)
Post-migration, turning scrutiny towards infrastructure platforms like HashiCorp Terraform allows us to streamline operations and cut unnecessary configurations. Evaluating API gateway efficiency and revisiting third-party integrations becomes paramount to maintaining compliance with standards like SOC2 and GDPR.
| Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|
| API Gateway Dependency | 34% CPU Overhead | SOC2 Partial |
| Legacy System Retrofitting | 27% Increased Egress | GDPR Missing |
| IAM Configuration Complexity | 15% Memory Inflation | SOC2 Comprehensive |
| Microservices Integration | 40% Throttling Costs | GDPR Partial |
| On-Prem to Cloud Migration | 45% Overbudget | SOC2 Incomplete |
We will perform an exhaustive audit of our current cloud expenditures and egress costs. Initial audit activities will include a thorough analysis of API dependency costs and vendor lock-in implications. Comprehensive IAM policies will also be evaluated to ensure excessive permissions and other vulnerabilities are not inflating our cloud bill. FinOps will lead this audit, working closely with DevOps to identify and categorize unnecessary data transfer and broader inefficiencies across our cloud architecture.
Technical debt accrued from rapid cloud migrations will undergo scrutiny, prioritizing areas where refactoring can yield immediate cost reductions. While maintaining our deployment frequency remains crucial, deliberately examining deployment configurations for egress optimization offers a balanced approach.
Compliance will not be overlooked. Verification processes will be put in place to assure that our operations remain within the boundaries of SOC2 and GDPR, mitigating any risk of incurring fines or additional operational costs due to non-compliance.
If any service is found unjustifiably redundant or an economic liability, consider deprecation. By addressing ballooning egress fees and API dependency costs, we preemptively counteract the financial impact of unchecked cloud expenditure growth. Therefore, the engineering teams must prepare for the outcomes of the audit, which may include immediate reconfiguration mandates or strategic service pivots to on-prem or hybrid solutions.”

1 thought on “Redefining Cloud Migration Navigating API Dependency Costs”