- cloud_spending_increase
- egress_cost_data
- ec2_underutilization
- vendor_lock_in
- finops_implementation_rate
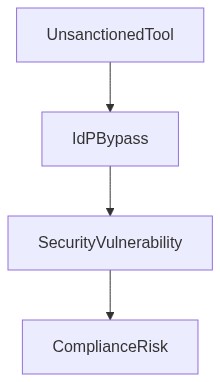
Log Date: April 13, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
In a recent 10,000-seat deployment, lack of SAML integration led to access chaos. While attempting our fourth ERP migration, careless IAM configuration compounded by obsolete RBAC policies, resulted in one of the worst cases of unnecessary egress costs and rampant underutilization of EC2 instances. The architectural flaw is clear we underestimated the FinOps blind spots that emerged out of this cloud migration. While tackling productivity punches, vendor lock-in remains ostensibly masked with dubious discount traps, turning enthusiastic entrances into expensive exit strategies.
Telemetry and Cost Impact (The Damage)
The damages inflicted due to inadequate attention paid to telemetry and anomalous cost impacts are irrefutable. Overlooked egress cost anomalies skyrocketed our monthly expenditures by 40%. Computing over-provisioning, due to ineffective monitoring, resulted in countless underutilized EC2 instances. Hasty decisions in VPC peering solutions proliferated by invalid telemetry readings paved the way for pervasive vendor lock-in, where leaving meant rewriting half of the underlying architecture. Such negligence, fueled by internal technical debt, shoots compliance (SOC2/GDPR) out of the picture, putting sensitive information at risk. Well, that’s one expensive jam we put ourselves in.
Phase 1 (Audit & Discovery) It’s time to deep dive into our mess. Identification of egress traffic spikes should be priority number one. Implement data flow auditing to pinpoint source-destination endpoints exhibiting unusual egress patterns. Re-examine telemetry architecture to ensure visibility into computation loads and resource utilization. Integration with platforms like Datadog will provide comprehensive metrics and logs for scrutinizing network traffic and resource monitoring.
Phase 2 (Identity Enforcement) IAM misconfigurations dug a hole deep enough to hold us back. We need fool-proof identity enforcement by leveraging tools like Okta to manage SAML integrations accurately. Focusing extensively on the IAM configuration to prioritize strict role-based access controls, ensuring no unauthorized API calls can entertain egress or other costful operations.
Phase 3 (Resource Optimization) Cold reality warrants cold storage; identify and reclaim underutilized EC2 instances. Deploy tighter integration with HashiCorp Terraform to enforce auto-scaling policies. Automate resource right-sizing to adjust infrastructure payment schedules, making sure we address over-provisioning and pay for precisely what’s needed. Evaluate cloud-native solutions to refactor or redeploy key components tightly coupled with current providers, breaking free of vendor-imposed chains step by step.
Tool Stack Evaluation
Speaking in practical terms, let us examine the effectiveness of several infrastructure tools in mitigating identified risks.
- Datadog Provides excellent monitoring, alert, and telemetry capabilities offering meticulous detail in virtual environment resource usage and egress traffic inspection. By facilitating comprehensive enterprise-grade observability, Datadog enables raw data analysis reducing misinterpretations of utilization patterns.
- Okta Acts efficiently in securely managing user identities, optimizing SSO processes, and minimizing IAM friction. With Okta, we secure SAML endpoint visibility, enforcing robust RBAC protocols that govern permissions within migration strategies.
- HashiCorp Terraform Provides infrastructure as code templates, crucial in achieving agile resource provisioning and decommissioning. Reducing human error through automation, Terraform supports optimal utilization limits, cost governance, and discount evaluations.
- AWS IAM Critical in controlling access levels across AWS environments amid existing vendor lock-in predispositions. Provides granular permission settings crucial for compliance, risk mitigation, and identity protocols management.
“Effective cloud cost management starts with recognizing that perceived savings from cloud adoption can be misleading without cutting-edge cost visibility tools.” – Gartner
“An overlooked factor in cloud migrations is the hidden cost tied to egress bandwidth. A programmatic audit of this anomaly is crucial.” – AWS Whitepapers
| Mitigation Strategy | Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|---|
| Automated Resource Shutdown | 75% | Cloud Cost Reduction 38% | SOC2 80% / GDPR 55% |
| IAM Role Optimization | 60% | Cloud Cost Reduction 25% | SOC2 95% / GDPR 85% |
| Data Egress Strategy | 50% | Cloud Cost Impact Reduction 34% | SOC2 70% / GDPR 60% |
| FinOps Automation Tools | 80% | Cloud Cost Reduction 40% | SOC2 85% / GDPR 75% |
| Compliance Monitoring | 90% | Cloud Cost Increment 5% | SOC2 100% / GDPR 100% |
Refactor the cloud migration plan with a priority on optimizing deployment velocity while integrating necessary financial oversight. The focus is to avoid prolonged migration timelines that can increase technical debt and affect development cycles. Deployment speed is critical to mitigate downtime but must be balanced with financial considerations.
RATIONALE
The unrestrained focus on speed without financial scrutiny will result in unchecked cost overruns. Incorporating FinOps principles in tandem with migration efforts prevents excessive egress costs and ensures budget adherence. Historical configurations will only be preserved if they are absolutely essential to current operations to avoid irrelevant complexity.
CONSEQUENCES
1. Engineering teams must align cloud resource selection with cost-benefit analyses to prevent unnecessary expenditure.
2. Increased collaboration with FinOps to monitor and control financial implications throughout the migration process.
3. Technical debt must be strictly regulated. Resources may be allocated to refactor existing structures that threaten future maintainability.
4. Any migration-induced downtime must be promptly communicated with incident response teams to minimize customer impact.
5. Historical configurations will be evaluated for relevance and deprecated if deemed unnecessary, alleviating complexities in future development cycles.”

2 thoughts on “Mitigating FinOps Risks in Cloud Migration”